
Lead Times and the Supply Chain Shortage
There are many signs that society is headed toward “back to normal.” Virus numbers are going down in many parts
At Imperium Data, we take pride in being your trusted IT solutions provider, offering a spectrum of services designed to catapult your business into the future. Our blog is a dynamic space dedicated to unraveling the latest trends, groundbreaking technologies, and insightful strategies that empower businesses to thrive in the ever-evolving digital landscape.

There are many signs that society is headed toward “back to normal.” Virus numbers are going down in many parts
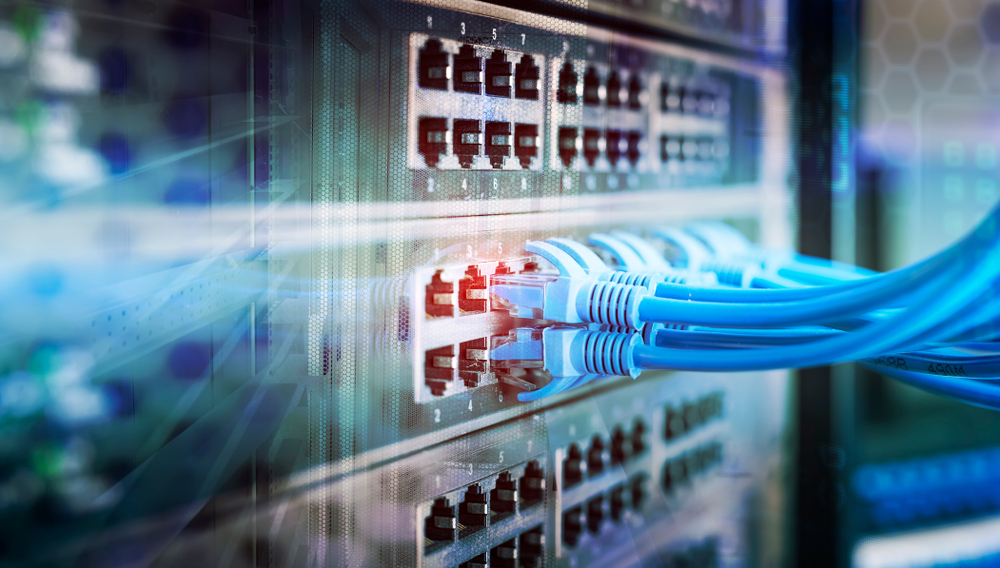
Understanding the Distinction: Routers vs. Switches Routers and switchers are the bridges that connect computers, devices, or other networks. They

Do you ever log in to an online account and are forced to provide more than a password? Sometimes we

Enhancing Work Efficiency: Employee Productivity Tracking The workforce has changed, and management has to follow. With 1/3 of the United

Enhancing Security with Remote Lockout and Data Wipe Features Imagine this – You love your computer and find it to